Traditional intrusion systems are designed to detect and report a break-in. By integrating a Phantom Fog compressed particle module with the ELK E27 Alarm Engine, installers can add an active theft deterrence layer designed to disrupt criminal activity while an intrusion is in progress.
Using the E27’s powerful Rules Engine and programmable outputs, the system can coordinate fog deployment with sirens, lighting, notifications, video recording, and other automation actions to create a more aggressive response to unauthorized entry.
Key Benefits of the E27 + Phantom Fog Integration
Immediate Visibility Reduction
Once activated, the fog module rapidly fills the protected space, making navigation difficult and reducing the intruder’s ability to locate merchandise, equipment, or valuables.
Flexible Activation Logic
Using E27 Rules, installers can precisely control when fog deployment occurs. Examples include:
- Burglary alarms while armed away
- Multiple zone violations
- After-hours intrusion events
- Panic or hold-up activation
- Verified alarm conditions
This flexibility helps reduce unwanted deployment while allowing response logic to be tailored to the installation.
Coordinated Security Response
The E27 can trigger multiple actions simultaneously, including:
- Fog deployment
- Sirens and strobes
- Lighting control
- Door locking or unlocking
- Video recording
- User and central station notifications
This allows the fog system to become part of a larger automated security response rather than operating as a standalone device.
Optional Voice Warning Integration
For applications requiring an additional deterrence layer, installers can optionally integrate the ELK-120 Recordable Voice Module with the E27 system.
The ELK-120 can play custom voice announcements before or during fog deployment, adding a stronger psychological deterrent than sirens alone. Example messages may include:
- “Warning. Unauthorized entry detected.”
- “Authorities have been notified.”
- “Leave the premises immediately.”
Voice warnings can be used as part of a staged response sequence, allowing the E27 to escalate actions as an intrusion event continues.
System Integration Overview
A typical installation may include:
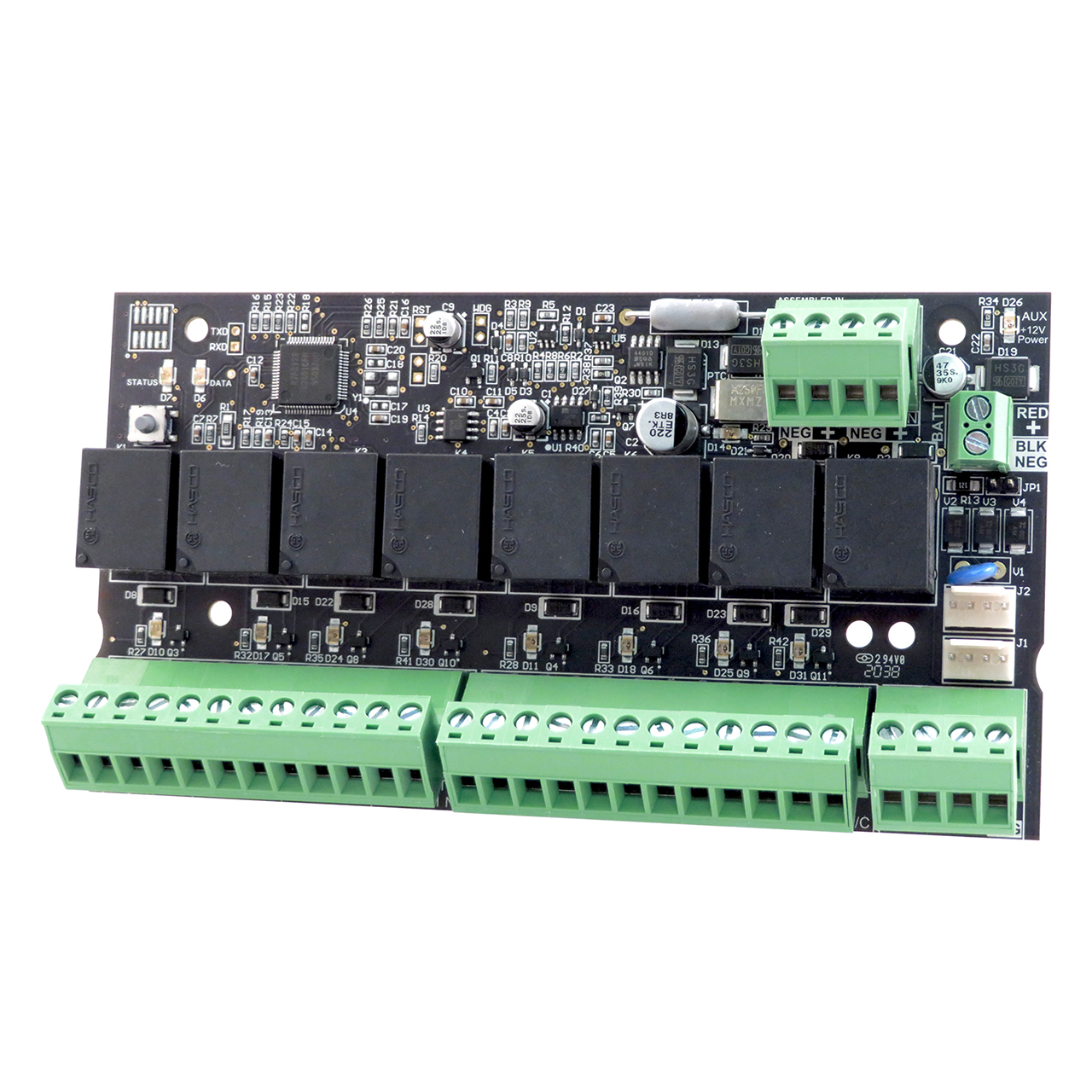
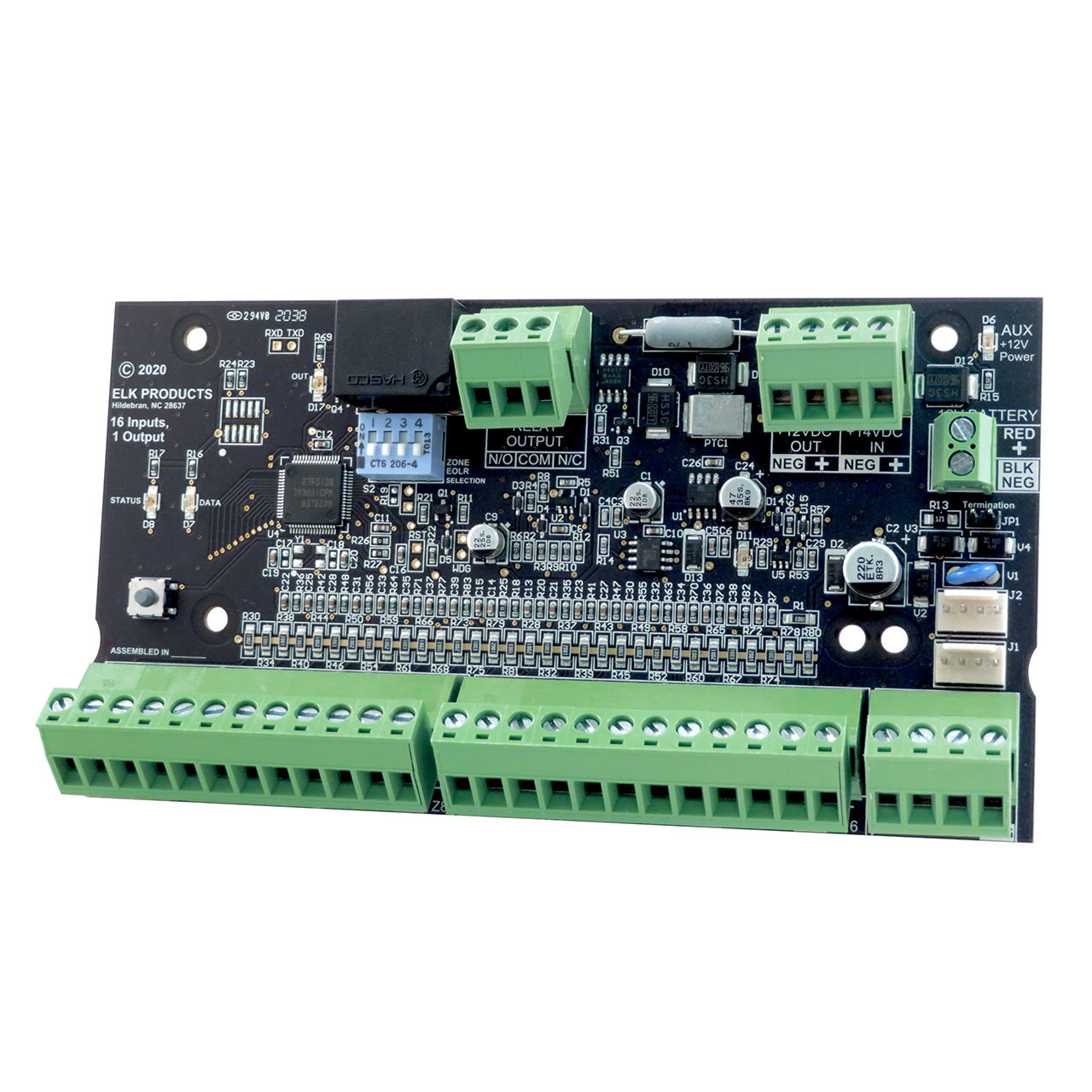
- ELK E27 Alarm Engine
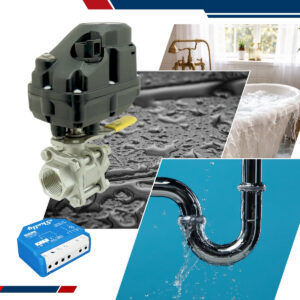
- Phantom Fog compressed particle module
- Relay/output interface as required
- Intrusion sensors
- Optional ELK-120 Recordable Voice Module
- Sirens, strobes, and automation devices
The E27 controls activation using programmable outputs and Rules programming. The E27 controls activation using programmable outputs and Rules logic. Relays from the Alarm Engine output expander are used to switch a negative voltage triggers to the Phantom Fog Enforcer System.
Example Wiring Diagram
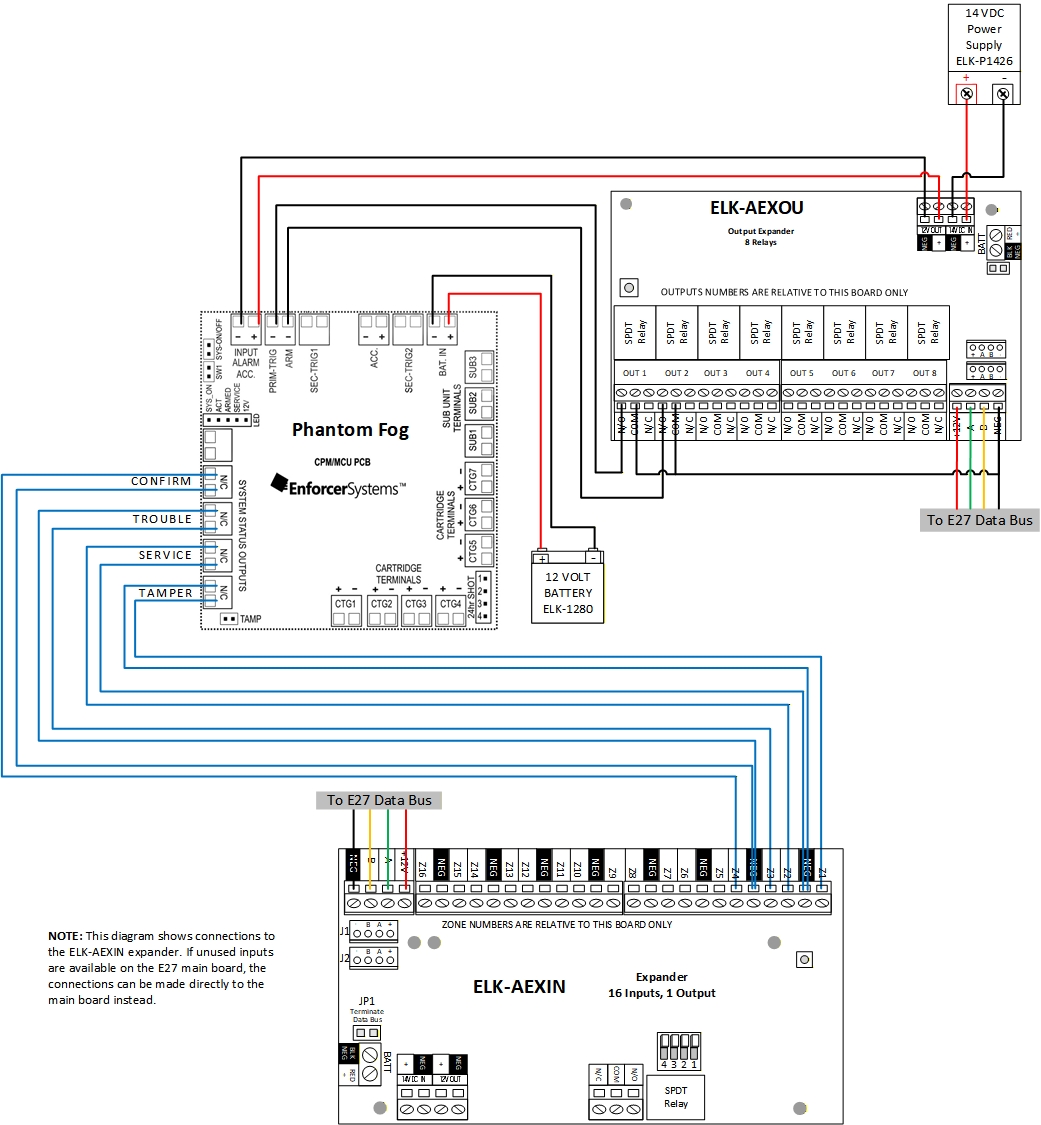
Wiring Details
Phantom Fog Enforcer System Connections
- INPUT: +12VDC and (-) up to 4 amps if 4 cartridges are used
- ARM: (-) Trigger Relay Output to arm the cartridges
- PRIM TRIG: (-) Relay Output first stage of activation,
- Final activation is provided by the onboard PIR
- CONFIRM: N/C Zone Input to confirmation that cartridge has been triggered
- TROUBLE: N/O Zone Input indicates system power or battery is below 10.8VDC
- SERVICE: N/C Zone Input indicates that cartridge has been activated
- Can only be reset with the reset button
- TAMPER: N/C Zone Input for cover tamper switch
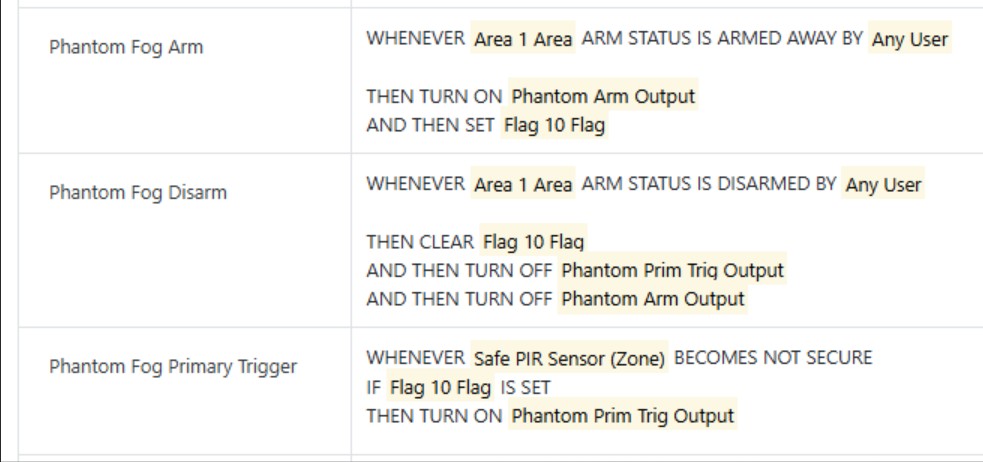
Rule Examples
The standard rules below arm the Phantom Fog system when Area 1 of the E27 is armed away; a relay on the E27 system is activated to trigger Arm terminal on the Phantom Fog system.
If a specific zone (Safe PIR) is tripped, a relay on the E27 system is activated to trigger the Prim Trig terminal on the Phantom Fog system, which puts the CPM unit into a ready to activate state.
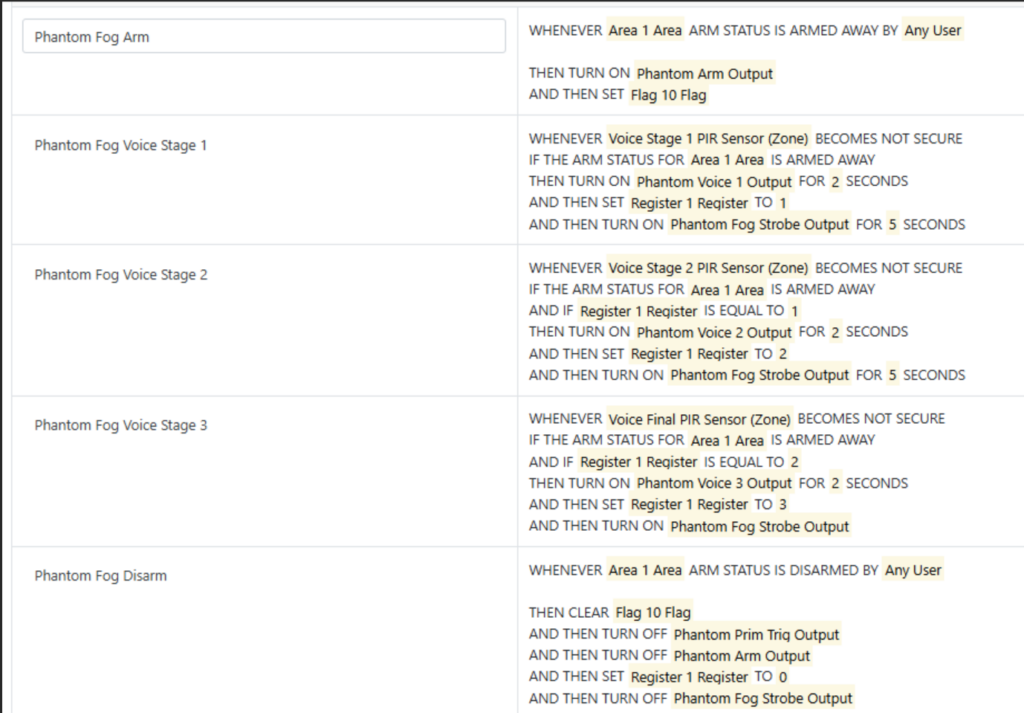
Voice Activation
These rules show a series of voice message activations for a layered response with verbal messages prior to fog activation.
Expanding the E27 Security Ecosystem
The integration of Phantom Fog with the ELK E27 Alarm Engine demonstrates how modern intrusion systems can move beyond notification into active theft deterrence.
By combining intelligent detection, automation, and visibility reduction — with optional custom voice warnings using the ELK-120 Recordable Voice Module — installers can deliver a more proactive security solution designed to help stop theft before significant loss occurs.